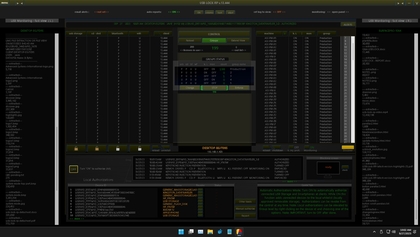
USB-Lock-RP
Centralized USB Device Management, Monitoring and Whitelisting to Protect Computers in a Network. USB Lockdown & Control Software to Block USB Devices and Lock USB Ports in Windows. Classified as USB Port Control for Enterprise.
- Paid
- Free Trial
- $1500.0 / One-off ("100 users")
- Official Pricing
USB-Lock-RP Alternatives
The best USB-Lock-RP alternatives based on verified products, community votes, reviews and other factors.
Latest update:
-
/buffstream-io-alternatives
Buffstream.io is a live streaming website that shows major sports and entertainment streams such as NFL, MMA, UFC, MLB, NHL, Boxing, Basketball, Football, MOTOR streams, F1 streams, and MotoGP racing stream.
-
/crackstreams-me-alternatives
CrackStreams.me is an online streaming website that lets you watch sports from Boxing to fighting, MotoGP to Formula 1, and cricket to football.
-
Try for free
Transform your IT service delivery with SysAid's seamless automation, ensuring a consistently exceptional experience for all users effortlessly
-
/endpoint-protector-by-cososys-alternatives
Endpoint Protector is a leading developer of multi-OS Data Loss Prevention (DLP) solutions
-
/user-inyerface-alternatives
A painful illustration of bad UX
-
/fightlive-cz-alternatives
Fightlive.cz is a streaming website that lets you watch live matches of major fighting sports like MMA, UFC, and Boxing matches.
-
/nba-streams-alternatives
NBA Streams is a live streaming website that lets you watch sports streams, including NFL, NBA, MLB, NHL, and NCAA.
-
/zabbix-alternatives
Track, record, alert and visualize performance and availability of IT resources
-
/how-i-experience-web-today-alternatives
Realistic web search experience
-
/duckduckgo-alternatives
The Internet privacy company that empowers you to seamlessly take control of your personal information online, without any tradeoffs.
-
/datadog-alternatives
See metrics from all of your apps, tools & services in one place with Datadog's cloud monitoring as a service solution. Try it for free.
-
/google-chrome-alternatives
Google Chrome is a fast, secure, and free web browser, built for the modern web. Give it a try on your desktop today.
-
/cloudflare-alternatives
Cloudflare is a global network designed to make everything you connect to the Internet secure, private, fast, and reliable.
-
/kaspersky-endpoint-security-alternatives
Our HuMachine™-based, Next Generation endpoint security delivers multi-layered protection for multiple platforms – including Linux servers and endpoints – to detect suspicious behavior and block threats, including ransomware.